Nzyme v2.0.0-alpha.1 has been released
Today, we are presenting the first alpha version of nzyme v2.0.0. Over the past 32 weeks, a lot of effort has been invested in rewriting large sections of the system. We’ve now reached a point of stability that allows for the release of this initial package. This blog post has everything to get you started and goes into more details about what to expect on the way to the final v2.0.0 package.
What works, what doesn’t work?
Alpha releases are by definition not feature complete. You will notice a lot of missing features and a very early version of the documentation. However, most of the things that are implemented, are fairly complete and ready to be used.
Here is a simple, incomplete overview of what is considered mostly complete:
- The new tap/node based architecture including the distributed multi-node model, message bus, etc.
- Automatic and UI-based TLS configuration for all web interface and API requests
- Automatic PGP encryption of sensitive data at rest including key management
- Deep multi-tenancy support across all functionality
- Authentication, user management, MFA
- System events and subscriptions
- System health console / Self-monitoring
- Monitoring and metrics, including Prometheus exporter
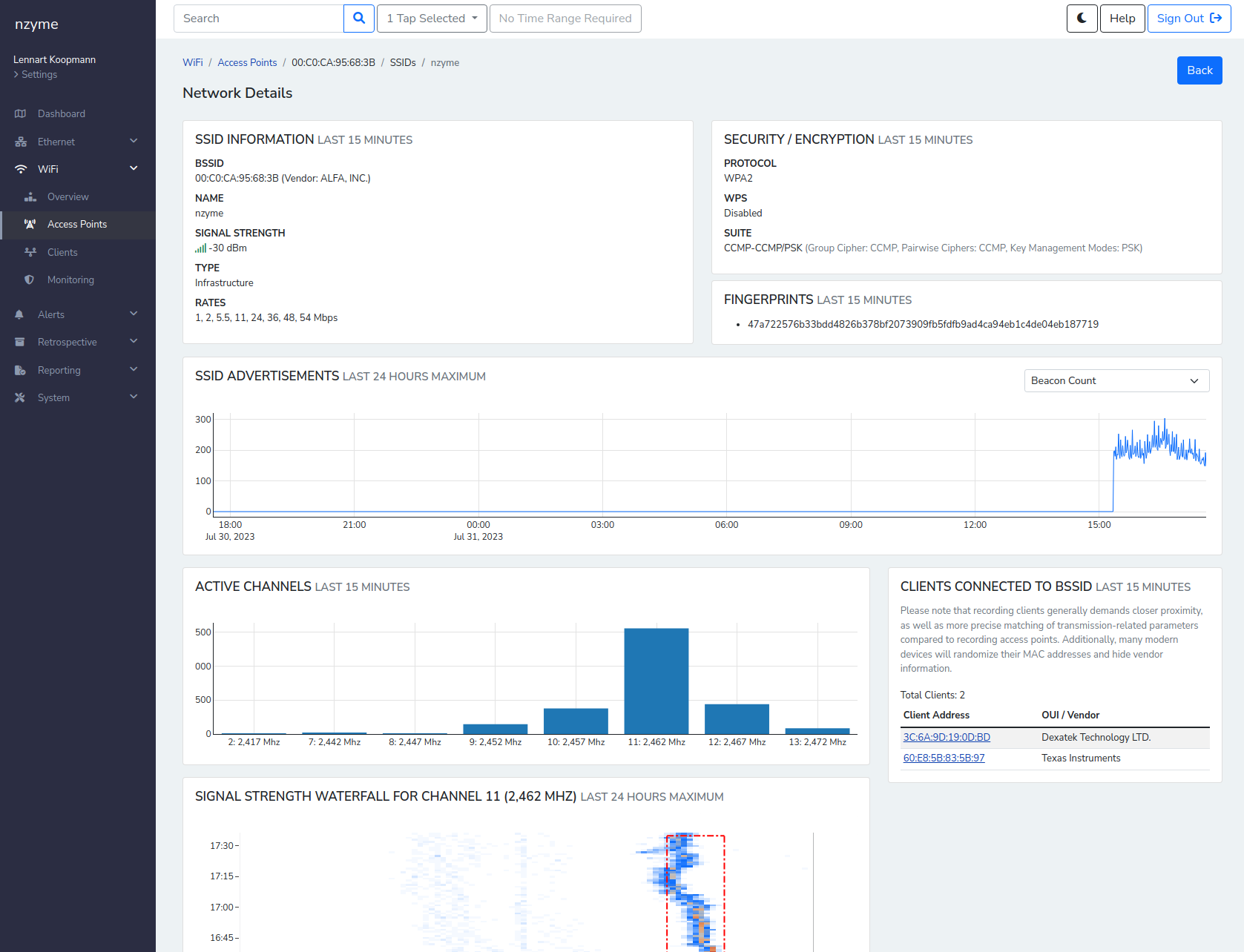
- WiFi data capture including automatic configuration of WiFi adapters without using any external dependencies
- Parsing and collection of security-relevant WiFi frame types
- WiFi environment overview and analysis
- WiFi network monitoring
- WiFi client analysis for authenticated and unauthenticated clients
On the flipside, here are some important things that are still missing:
- Alert triggers / notification methods for detection alerts
- WiFi deauthentication analysis and other detection methods, including detection of known attack platforms
- Long-term search/analysis of recorded data
- Dynamic, on-demand PCAP
- Real-time forwarding of recorded data to third party systems (Splunk, OpenSearch, Graylog, …)
- Most ethernet functionality, detection and visibility (Only a very high-level implementation of DNS and some layer 4 data so far)
The key point is that the architecture and configuration is unlikely to significantly change from here on out. If you
install alpha.1, coming releases will be very easy to install, likely with a single command.
Is it considered secure?
Yes, there are no known vulnerabilities, existing features have been designed to be ready for production from a security perspective and all dependencies are up-to-date.
The development closely followed OWASP ASVS Level 3. (“any application that requires the highest level of trust.”)
How do I install it?
Follow the installation documentation. Remember that the documentation is also still in an early state. A general understanding of WiFi and WiFi security will be very beneficial. Focus so far has been on the installation guides.
How can I help?
This release is meant to get people on the new 2.0.0 line of nzyme without having to start over when the next releases are coming out. You are the first users to try it out, and we are looking for any kind of feedback:
- What didn’t work, what bugs did you experience?
- What was confusing or seemingly unnecessarily complex?
- What is missing?
- What do you think should be changed?
Again, this is an early release and no feelings will be hurt.
You can file issues on GitHub, join the nzyme Discord or post in the discussion forums to provide your feedback or ask questions.
What’s next?
The next phase is to re-implement nzyme v1.x WiFi alerting, detection and analysis functionality. You can expect a substantial
alpha.2 release within a few days.
What about the private beta program?
While the release and all community resources are of course accessible to anyone (except certain countries, including the Russian Federation and Belarus to the extent technologically possible), a smaller group of users has been selected to participate for closer collaboration and feedback cycles. You will receive an email shortly if you have been selected.
Again, everyone else is invited to install this first release. There will be plenty of attention for everyone who has feedback, problems or questions.